Disassociating Networks
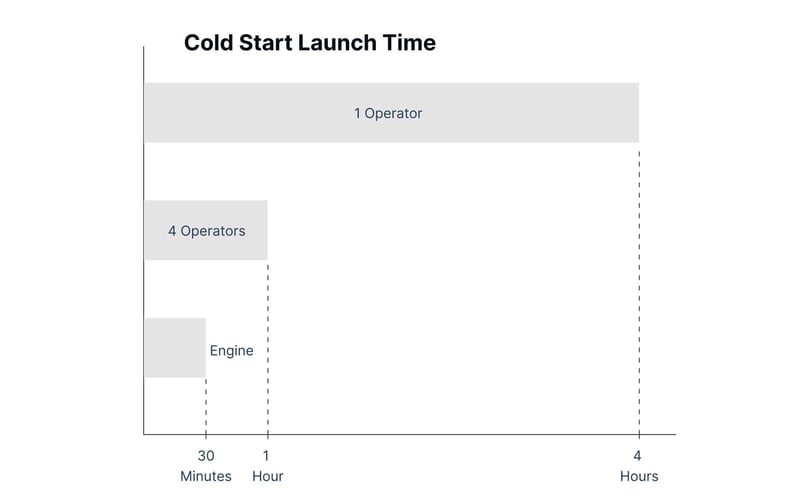
The bottleneck in the supply chain of Disassociating Networks is not a personnel problem, it is an automation problem.
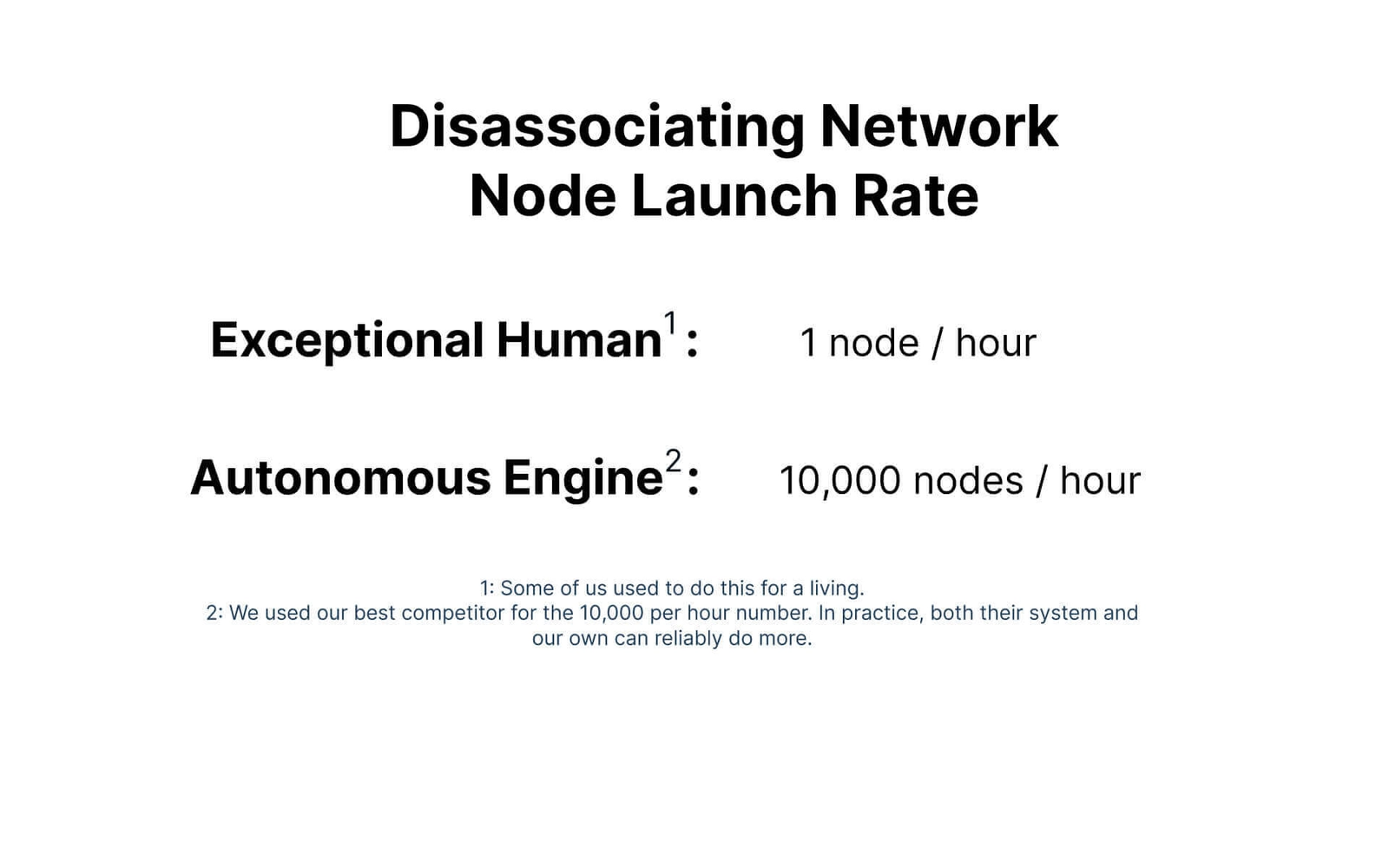
What you need is an autonomous launch and maintenance engine (an 'Engine' for short).
Resilience
React in time
Disassociating networks start to grow stale unless at least one node within them is replaced roughly once per hour. This limits the number of networks a team working manually can sustain to 1 network per three people (or two, if shifts are lengthened to 12 hours). This leaves such teams susceptible to being overwhelmed by demand precisely when they are needed most. In contrast, Engines can launch thousands of networks into a stockpile and maintain them automatically. The result is that you can have a warehouse of networks at your disposal which you can deliver within 30 seconds of when they are requested.

Optionality
Respond at scale
Properly designed, an Engine can not only launch and maintain networks, but also create copies of itself to accelerate the tempo of network creation exponentially. Assuming an infinite supply of servers, one Engine could spawn over 17 million networks within the four hours it would take a person to set up a single comparable network manually. The point here is not to say such a number of networks is necessary but, rather, that the maximum practical limit of networks that could be launched globally is now within reach of those with commercial off-the-shelf tools. You should have them too.
Conservation
Preserve Resources
The number of people, skills, and credentials involved means that a manually-built disassociating network typically costs $400k to $500k per year. This price point is beyond the reach of the commercial world, though the need for such network’s flexibility and defensive characteristics has increased over the past six years. Engines were invented in the early 2010s to bridge this price gap. Competition has done the rest – with an Engine-launched network of equivalent capabilities to those built manually for military use costing $25 to $30k per year.


Customizability
Focus the team on tailored work
Automation gives people time to do the tasks machines cannot. Imagine what your team or contractors could do if they were not conducting network tradecraft by hand.
Where to use disassociating networks

Comms in contested urban environments
This system, known as Hummingbird, solves the very specific problem of reducing the risk of teams or drone swarms working in contested urban settings exposing themselves through their communications. Hummingbird ties into commercial cellular networks, then links into a temporary moving target defense network composed of a combination of medium breaks and commercial cloud infrastructure to disassociate the assets in the field from the people with whom they are communicating, while also making the signal appear to be innocuous.

Intelligence gathering and disassociation
This system protects the context, as well as the content, of communications. While encryption serves to prevent an adversary from knowing precisely what words are said over a video conference, chat, or call, the fact that a certain set of entities or persons are communicating in an encrypted manner at a given time can, itself, be sufficient to infer what actions will be taking place. This system also enables persona management and intelligence collection without fear of burnback by disassociating the user from their activity.

Remote access
This system serves to provide secure, resilient communications networks for contractors needing to remotely access (for maintenance or control) equipment in the field. In such situations, the systems must address three competing needs simultaneously in order to be effective: Foremost is that the connection must be stable, fast, and efficient to use. Second is the need to disassociate the maintenance teams from the equipment they are servicing to prevent an adversary from locating the positions and types of equipment in the field. Third is preventing malware that may have reached computers controlled by maintenance contractors from traversing into the equipment being maintained.
What to ask from industry
Rapid launch time
Without human intervention, can launch a disassociating network in under 30 minutes.
Performance at scale
Can launch and maintain at least 4,000 virtual machine nodes simultaneously.
Scheduler
Can launch and maintain at least 4,000 virtual machine nodes simultaneously.
Rapid connection time
Can connect an authorized operator to a single use network in under 30 seconds through a pre-built network.
Multi-cloud
Can traverse three or more different commercial clouds.
Cycling
Automatically cycles components without breaking the connection.
Virtual desktops
Provides virtual desktops as intermediary units.
Screen recording
Provides screen recording and over-the-shoulder viewing capabilities.
Medium breaks
Allows for the addition of medium breaks (switches from one protocol or transmission medium to another) into the network.
Colorless core
Colorless core (identical encryption level for all transmissions).
Blanks
'Blank' / Customization-ready components.
Freestanding engine
Controller-agnostic / freestanding launch engine option.